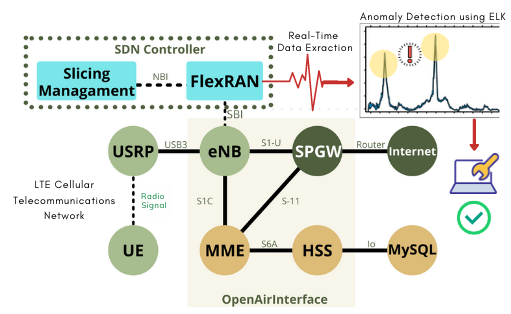
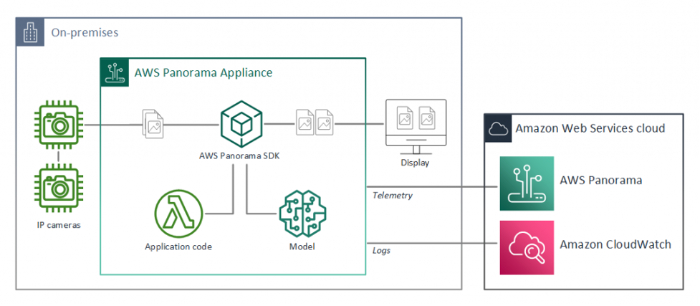
Performance Evaluation of Anomaly Detection System on Portable LTE Telecommunication Networks Using OpenAirInterface and ELK
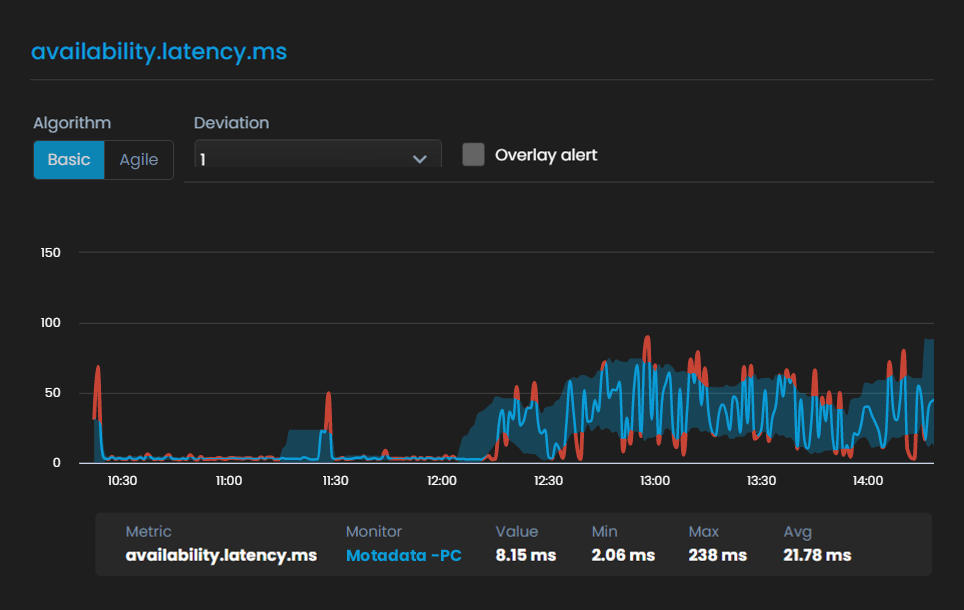
How to perform anomaly detection in time series data with python? Methods, Code, Example! | by Yu Rong (Tammy) Tsao | Medium

Anomaly network-based intrusion detection system using a reliable hybrid artificial bee colony and AdaBoost algorithms - ScienceDirect
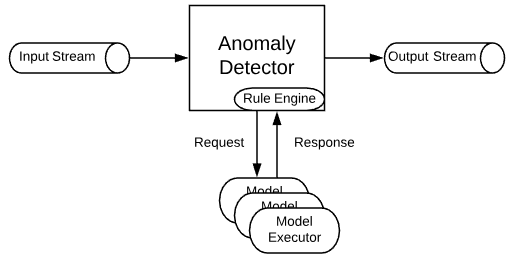
How We Built an Automated Anomaly Detection System onto a Streaming Pipeline - Salesforce Engineering Blog

What Is Network Behavior Anomaly Detection? Definition, Importance, and Best Practices for 2022 - Spiceworks

Improving Predictability of User-Affecting Metrics to Support Anomaly Detection in Cloud Services - IEEE Access

Anomaly detection in the context of long-term cloud resource usage planning | Knowledge and Information Systems






![PDF] Network Anomaly Detection System using Genetic Algorithm and Fuzzy Logic | Semantic Scholar PDF] Network Anomaly Detection System using Genetic Algorithm and Fuzzy Logic | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/aa1eb3de066b9640053708d7c3ce2fa94848f608/17-Figure2-1.png)